Content Type
Profiles
Forums
Events
Everything posted by NoelC
-
Throughout time, the number of processes to support my empty desktop, with my favorite tweaks and "to work" software: XP: High teens. 100 MB. Vista: 30 or so. 800 MB. Win 7: 34. 1 GB. Win 8.1: 42. 1.2 GB. Win 10: 120. 4 GB. 3x the processes prior versions had to rock, just to get anything done. Says it all right there. No wonder it really doesn't seem to run any better on modern hardware than prior versions did on the best hardware of 7 years ago. And you can't really trim it down any more, for several reasons. Back when we thought Vista, Win 7, and Win 8.1 were bloated, we simply didn't know what True Bloat was. -Noel
-
Sigh. End of an era I guess. Thank goodness for developers like Big Muscle who gave us Aero Glass for 10 years longer than we could have hoped to have it. I'm not quite ready to take my systems to v1909 yet, but it's inevitable. -Noel
- 409 replies
-
- Win10
- 10.0.14393
-
(and 1 more)
Tagged with:
-
Repairable doesn't make profit from selling new ones. Competition tends to pressure everyone to make better, higher quality products, but when EVERYBODY notices that if they ALL "save a little bit" on their manufacturing costs and lower quality, they sell more product. It used to be possible to actually TELL if a product had higher quality. Nowadays making things bright and shiny and still cheap is a science. Light bulbs, for example... In the latter part of the 20th century it wasn't uncommon to still find incandescent light bulbs that had remained working and in service since the early part of the 20th century. Ever notice that lately - before the era of CFL and LED bulbs - incandescent bulbs would last EXACTLY the number of hours listed on the box (i.e., usually a few weeks to a few months of use). That's not coincidence. It's engineered-in. We'll skip CFL bulbs, but then LEDs came out, promising tens of thousands of hours of service. We all bought the ones that were 10x as expensive as an incandescent bulb thinking, "Gee, maybe I won't ever have to replace this again!" Ever notice how you're now replacing your LED bulbs WAY sooner than you thought you should have to? Sigh. Don't get me started on plumbing and faucets. Same deal. Our parents (or grandparents if you're a young whippersnapper) loathed the idea of planned obsolescence. They didn't want us to have to live in this world where our $#!+ just breaks all the time and is unrepairable. Imagine what we could do with the world if we had the time to think instead of fixing stuff that shouldn't be broken. Another thing they worried about, and which came to pass anyway: Paying by the month for things, instead of just buying them once and owning them. We still worry about software subscriptions, but make no mistake: We're already there or well on our way there for just about every piece of tech we use, INCLUDING software. -Noel
-

Is there a *real* fix for GUI blinking/flickering issues?
NoelC replied to UCyborg's topic in Windows 10
Pretty much since I cut the legs out from under the Microsoft security suite (using WinAero Tweaker) I've stopped seeing Aero Glass getting trashed. And no, I don't think it's a crash count disablement thing. Windows Reliability doesn't show failures, and I'm not accumulating mini dumps. -Noel -
Win 10 v1909 essentially IS v1903 with some run time switches thrown. Same underlying OS build. As those of you who have been through the upgrade have seen, it was only a minor install that didn't take long to download nor restart. Not an in-place upgrade at all, but just another update. I admit NOT swapping out the OS underpinnings is perhaps the first impressive thing Microsoft has done with Windows in a long time. Hurrah! It would be awesome if BigMuscle would rebuild an optimized version of Aero Glass for Win 8+ that loosened the compatibility check and allowed v1909 just the same as v1903, without the dialog, though we can of course hit the [Cancel] button for now as a workaround. Let's hope he still has the interest to continue to develop Aero Glass for Win 8+. BigMuscle, if you're listening, it would also be cool if you'd add a version check circumvention based on a registry entry (assuming you don't already have one) just in case something like this amazing continuation of Windows compatibility should ever happen again. Thanks! -Noel
- 409 replies
-
4
-
- Win10
- 10.0.14393
-
(and 1 more)
Tagged with:
-
Some marketing goon said "thinner is better" and for some reason people listened. Now we have laptops, tablets, and phones that have gotten so thin you can hardly use them or even hold them. So thin a keyboard can't possibly be ergonomic. So thin you drop them (after which of course you have to buy a new one). And let's not forget that the keycaps can get snagged and pulled off requiring no less than the replacement of the entire device. Not long ago I got a heavy, thick Cat S61 phone with grippy rubber and raised edges that doesn't try to slip out of my hand or pocket every chance it gets, and if it DOES crash to the ground it survives. The battery lasts most of a week. Turns out it wasn't just a frivolous thought that extra thin, slippery devices are optimizing for something decidedly different from usability, and that when someone makes usability a design goal it actually CAN be achieved. And yeah, there are only USB-C ports on new MacBook Pros (not sure about other models). I have a nice little short female USB-A to male USB-C adapter cable that has saved my bacon a few times. As a society we're not only not learning from the past, but the folks who seek to sell us stuff over and over are actively changing things away from stuff that worked just fine. And here we are applauding and rewarding those who make such changes by buying even more crap from them. Kinda seems like we consumers ought to try to be smarter about what we throw our money at, eh? I think that would entail never listening to any Marketing info - something that's clearly impossible. -Noel Welcome, my son Welcome to the machine What did you dream? It's alright, we told you what to dream -Pink Floyd
-

Is there a *real* fix for GUI blinking/flickering issues?
NoelC replied to UCyborg's topic in Windows 10
I've found that disabling most of the "gee whiz" new features tends to make Windows more pleasant to use. That being said, my Taskbar on my v1903 system now flickers when I type into the Open Shell search box. Sigh. My icons go to weird places intermittently about every month or so when I connect into a multi-monitor system from another multi-monitor system with the same monitor layout. Aero Glass just goes away after a week or two and that ugly flat stupid Windows look returns. Aero Glass has to be reinstalled. I presume it's being scrubbed out of the system by Microsoft in the name of "security". What hare-brain came up with the idea that stuff has to get worse and more irritating to use as time goes on? -Noel -
Change is inevitable. Necessary. We have increasing needs for tech. Embracing change is not what this is about. Creating incompatibility to suit business goals is not right. Our parents were appalled at planned obsolescence. Now we're told to accept it. Embrace it. Our tech becomes obsolete even before it can wear out the batteries! Using Fear, Uncertainty, and Doubt in the name of "security" as a way to herd people into doing what they would not do is deplorable! Yet for the most part we find ourselves powerless, because people who predicted this and warned against ceding control were marginalized. Ridiculed. Pushed aside. -Noel P.S., the latest incompatibility I've noticed: RDP from an older system into a Windows 10 v1903 system and your mouse jumps around when the cursor graphic is changed. It didn't do that remoting into v1809. The protocol has been good enough - indeed excellent - for decades. It doesn't have to change. Aero Glass just gets shut off and requires regular reinstalls, even though it works fine. Presumedly because some jerk inside Microsoft wants us NOT customizing our Windows look, because that goes against their current Marketing direction. Who the &%$& do they think they are? We could talk about the atrocities Apple is pushing on people... No more 32 bit programs. No more putting things where you want them on your disk. Can't reach your Documents area even though you've shared it? Oh, right, that's security. P.P.S., I'm typing this on a perfectly good Digital LK250 keyboard circa 1985. And there isn't a better one built today. Stuff doesn't HAVE to go bad just because it's tech.
-
For figuring out what's multi-threaded and how well programs use the available resources, I like Process Hacker 2, but even regular old Task Manager will show you a decent heat map of actual CPU usage. A program could make tons of threads and not really use them effectively. Don't look at counts as any kind of real indication of goodness. If a program cranks up all the cores (and hyperthreaded logical CPUs) so they're truly busy when it's cranking through your data, then you know it's doing actual (and hopefully effective) multi-threading. Traditionally well-threaded applications I can think of off the top of my head, include Photoshop's Radial Blur filter, Visual Studio when building big projects, MalwareBytes, my own Photoshop plug-ins... There are I'm sure a few others I'm forgetting. Oh, I guess Passmark Performance Test will crank up all the CPUs when testing. Windows itself does a decent job of taking advantage of multiple threads. One thing I've always noticed is that with in excess of 12 logical processors you can really open lots of windows without feeling the load too badly. If you have a really busy computing day this can be very handy. On the other hand, closing 50 windows before leaving at 5 may mean you leave at 5:30. :) -Noel
-
Yeah, sure - but that only accounts for maybe 30 of them. There's still another 20+ to go. -Noel
-
I'm pretty sure that's a given with Windows 10 - i.e., it's built in to the window compositing softare and you can't get around it. I've just decided to get used to the buttons being the same size. I'm very pleased to say I'm able to get Aero Glass to work now with v1903, and the same theme atlas I had put together a long time ago still works pretty darned well. -Noel
- 409 replies
-
1
-
- Win10
- 10.0.14393
-
(and 1 more)
Tagged with:
-
On the subject of performance, it's funny... At this point I have two Dell Precision workstations I switch back and forth between to do development work: My personal workstation, a circa 2012 Precision T5500 dual Xeon system with 12 total cores, 1333 MHz DDR3 RAM, an SSD array capable of 1.6 GB/second throughput, and a modest 3 year old nVidia Quadro P2000 graphics card. This one runs Win 8.1, updated to December 2017 (i.e., pre-Spectre/Meltdown hooey). My office workstation, a new circa 2019 Precision T7820 single Xeon system with 6 cores, 2666 MHz DDR3 RAM, an M.2 flash array capable of 4 GB/second throughput, and a rompin' stompin' new nVidia Quadro RTX 5000 graphics card. This system runs Win 10 v1809, fully updated. Both systems are tweaked and trimmed as best I can to do engineering work - within the constraints of what each OS will stand for maximum leanness and performance. Windows 8.1 stands up to FAR MORE such tweaking than Windows 10. For example, when quiet my Win 8.1 setup has about 42 processes running to support an empty desktop. My Win 10 setup has to rock 100 processes just to sit there idle (and that's down from some 130+ out of the box)! Friggin' bloatware. Since most software is still single-threaded and dependent on I/O speed and RAM speed, you'd think the MUCH newer system, even with fewer cores, should really run rings around the 6 year older system, right? It is not so. Using them interactively, frankly - and surprisingly - the two systems actually feel about the same to use. While neither is a slouch, for the things that benefit from more cores the older system even feels smoother and more responsive. It doesn't "load up" as easily nor feel as sluggish when I fill up the Task Bar with work. Conclusion: Windows 10 and all this Windows redesign by patching BS done in the name of "Security" has soaked up and erased 6 years of computer performance advancement. Seriously. -Noel
-
Seconds release for v1809 seems to work perfectly. Haven't had a DWM reset since installing it. Thank you for making Windows a little more tolerable. -Noel
- 409 replies
-
2
-
- Win10
- 10.0.14393
-
(and 1 more)
Tagged with:
-
I replaced aerohost and DWMGlass with those from the .7z and all seems well so far. Haven't seen a new crash after the update. I did see several related to Taskbar Live Previews with the prior revision. -Noel
-
I'm making the best of the situation I have been dealt; I have to have Win 10 on my office workstation. Not surprisingly, all the efforts I've put into training Win 10 to be a decent workhorse are paying off. I'm not delirious; it's actually possible to derive some value from Win 10. It's bloated and not my first choice - but it's not really worse than a lot of past versions. With the For Workstations variant (and Pro) the local group policy editor can be used to set it to install updates only when you want them. There are decent sites on the web that seek to inform whether the current crop of updates is "good enough". One I like is AskWoody.com. -Noel
-
Got Windows 10 for Workstations v1809 on an office computer (and I still have Win 8.1 on my home workstation). Been running Windows 10 in the office since the start of the year. It's not bad. I like the dark theme. And it's been stable. So far just once I have had explorer do something to the wrong file and I'm sure I didn't fat finger the keyboard or mouse. And it seems like Office notifications take a little while to show up sometimes. But no other failures. The machine's a beast, so mostly it doesn't matter that between 130 and 180 processes are running where 40 or 50 would do. I definitely think performance suffers from the bloat. Though I sometimes wonder how fast it would be if it were running a lean, trim OS on that same hardware. -Noel
-
General instability of the ATI software isn't something I'm willing to ignore, and anyway I had an opportunity to change to a much more powerful GPU, which has turned out to be perfectly stable. Ultimately, the version of Aero Glass I am running has been very solid, so I have not tried the new build. -Noel
-
With a brand new workstation with Win 10 v1809 I had some initial instability, but when I changed from ATI to a nVidia graphics card on the 24th it's been very solid with the released version of Aero Glass. If I'm not experiencing any problems, would it be useful/helpful to test the latest debug version? -Noel
-
Aero Glass 1.5.9.1479 working very solidly for me here with a reasonably well-tweaked Win 10 v1809 (with no Apps). I've noticed the performance seems better than with past debug versions. Big Muscle, did you add some optimization? Whatever you did, thanks; it's quite pleasant to work with. Thank you,. https://Noel.ProDigitalSoftware.com/ForumPosts/Win10/17763/Win10DesktopWithAG.png -Noel
-
A Haswell-based system running Win 7 and serving as a small server is working perfectly. And when I say perfectly, I mean it doesn't even log anything more than an informational message in the System Event Log for months at a time. It runs forever without fault, does its job with aplomb, has plenty of free storage, and will not likely be asked to do any more in the next few years than it already does. It's layered with much more (and smarter) than typical security and its usage is such that it's not at risk from typical things like web pages loaded into a browser and downloads by a user. Likely it won't need updating until the hardware actually fails. Since it's high quality server hardware, that won't be for years. So... To update it or not? I'm seriously leaning toward not. Ever again. My father tried to teach me, "If it works, don't fix it". I'm knowledgeable enough about networking and OS operations that I'm not affected by FUD and hype such as "OMG, if you don't update you'll be infected for sure". I know how it could be attacked, and it's just very, very well protected. I always try to keep in mind that Microsoft hasn't fixed anything since Win 7 went off mainstream support, and the only thing they've done lately is to slow the OS down... Even if the heaviest patches are disabled (GRC InSpectre, anyone?) it's still slower than it was in 2017. I can't believe I'm even considering whether to run another Windows Update on it. The social engineering that has brought us to this point and made us feel dependent on Mother Microsoft to keep trickling out fixes for vulnerabilities they originally built in is mind boggling. What price, (a false sense of) security? -Noel
-
I'm not talking short term! I think I began to sense the change when Bill Gates stepped down from active management. That was a while ago, for sure. They spent a lot of years throwing things together then tidying it up later, but if you followed the "wait until Service Pack 1" (at least) philosophy, Windows has been a pretty good workhorse. I still remember when it went from something that had "reboot fairly often" built into its design to "runs virtually as long as you want" - which for me happened around SP2 (I think it was) of Vista. I got work out of Windows 3.1 for Workgroups and all the versions since, and to this day I still get a LOT of work out of Windows 8.1 - of course after taming its desire to be something it's not. That taming just doesn't work as well with each subsequent new version. Inertia took Microsoft a long way and is still carrying it along, but they're losing sight of the fact that the world needs Windows to be the serious, no nonsense business system that actually facilitates people's work on inexpensive hardware. Even though they made a lot of money being that, now it just seems like they want to facilitate their own updates and bloat, and have all but forgotten people don't run Windows just to run Windows, but to actually DO things. There is a helluva lot more a lot of folks need to do besides check Facebook and Twitter! You have to admit, the no-nonsense Windows 7 update philosophy - putting YOU in charge - was way more "good, serious computing experience" than this modern "Windows as a Service" BS where they take over whenever they choose to. And who said it was okay to change our settings, or delete our files? That was the realm of MALWARE before they started trying to social engineer people to change the way they look at computing. Even now - in the very latest versions of Windows 10 - we see them adding things like "WaaS Medic" and being ever more aggressive in taking over, while of course they say they're not. Just try to disable certain services and see how long that lasts. So yeah, they're not the company they used to be, not even last year. -Noel
-
We are supposed to all want Microsoft's patches without thinking. They work hard to create this mentality, in order to herd users ever more effectively. Fortunately (they would say unfortunately) I actually DO think, as do you (or you wouldn't be here reading). I think about these so-called "vulnerabilities" - some of which have never been seen in the wild - and what I can do about them. Knowing how things work is better than not knowing. I am most certainly NOT helpless in the digital world. I don't run software "from the wild" without vetting it. I have surrounded myself with a network environment that practically and substantially reduces the risk I'll visit a web site that will try to infect me or take data from me, while at the same time shunning the "run-of-the-mill" approaches that provide only marginal security. I resist "cloud" software that wants to update itself all the time. I don't want the "latest", I want the "most stable" that does what I need. My systems run for months 24/7 without faults, however hard I use them. Unlike most folks, I actually measure performance objectively, and can tell when the OS or application efficiency changes. I always realize there are tradeoffs - security is never a purely "more security is better" thing. I haven't had malware turn up on a MalwareBytes scan - ever, so I guess what I'm doing is effective. That said, I always look for ways to improve. Possibly most importantly: I never allow myself to get a false sense of security. If I do something stupid, and one of the things I've set up protects me, I still beat myself up over doing something stupid and strive not to do it again. If you look at the pricing of high-end systems - say, workstation prices at Dell - depending on how close to the top end the hardware is, you can see that computer systems delivering even just 10% more compute performance can cost literally thousands of dollars more. Why would I want to intentionally turn my system now, to mitigate vulnerabilities for which there are no known exploits yet, into a system that performs as poorly as the ones I passed up when I chose to pay top dollar? I simply don't subscribe to the sentiment "you WILL become infected if you don't patch to the very latest OS code", because Microsoft is not the company they used to be. It is no longer as high on their priority list to deliver a good, serious computing experience. There is no guarantee that a patch from Microsoft delivers better code than what it's replacing. Time has shown that they can (and do) deliver instability and even new vulnerabilities. I always try to gauge the tradeoffs. And let's not forget that they've let much of their testing organization go. It's clear Microsoft wants to bring everyone under their control (which invariably involves updating to their latest software) and they're using every trick in the book to get you off your old system where they do not yet have that control. They do not care whether your existing system/hardware works worse for what you need it for; you're not paying them to keep it. You WOULD, however, be paying them if you replace it. Microsoft software, even the very mature versions, is nowhere near optimized as well as it could be. There's no reason we have to expect it to get less efficient as newer versions are released. It should steadily be going the other way. For example, I've seen with my own eyes that their latest compilers are delivering faster and faster instruction sequences for the very same source code. Why aren't their OS patches/releases speeding up the system? It appears for every 10% improvement they make, they layer on 20% more junk. How many processes does Windows 10 have to run just to host an empty desktop for you nowadays (hint: well over 100)? Hosts? Brokers? Medics? Bleh. I have some systems from which I don't demand the utmost in performance, and for which security is a greater concern, and I've got them completely up to date. Others I have stopped at the December 2017 patch level, because there are significant disadvantages, while at the same time Microsoft just hasn't delivered any improvements that matter. Your mileage may vary. Just make sure to know what it is. -Noel
-

Thank You Big Muscle For New Aero Glass Build 1.5.9
NoelC replied to 666_peter_666's topic in Aero Glass For Windows 8+
...and... Now with the end of August update Windows 10 is up to 17134.254 and I saw my donation-enabled copy download symbols again. SYMSRV: dwmcore.pdb from http://msdl.microsoft.com/download/symbols: 3279872 bytes copied SYMSRV: PATH: C:\AeroGlass\symbols\dwmcore.pdb\7E2FFBA889DA4A0EEEC178DF672CE1B81\dwmcore.pdb SYMSRV: RESULT: 0x00000000 DBGHELP: dwmcore - public symbols C:\AeroGlass\symbols\dwmcore.pdb\7E2FFBA889DA4A0EEEC178DF672CE1B81\dwmcore.pdb -Noel -
And make sure you know that using a non-Microsoft-signed theme can get you into trouble when you upgrade the OS... You'll either have to be careful to remember to disable re-theming before running through an upgrade or be sure to be able to restore your system if you get a black screen of death. -Noel
-
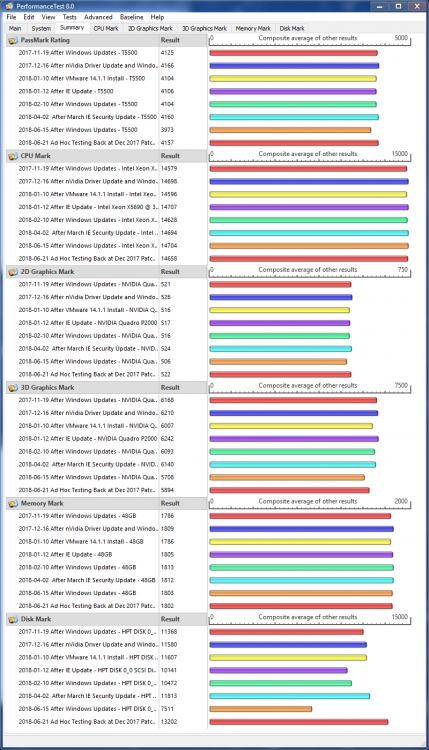
For what it's worth, I always benchmark my systems with Passmark PerformanceTest after I've made any changes such as updates, driver installs, etc. I have years of stored results, so I can say whether and when various slowdowns occurred. This system (now 5 years old) has never run quite as efficiently as when I was running Windows 7. But that difference is small and I do enjoy the few things Win 8.1 has brought to the party. With Aero Glass it's a very good system. Plus it runs various other Windows versions in virtual machines quite well, so I have a "have cake and eat it too" situation. -Noel