Search the Community
Showing results for tags 'Powershell'.
-
PowerShell 7 on Windows Vista Extended Kernel done properly So here's how to install 64-bit PowerShell 7 on Windows Vista with Extended Kernel. You MUST use EXACLY version 7.2.2. If you want to know why is that, go to the section why 7.2.2?, but for now here's a Quick step-by-step guide: 1. Install Windows Vista Extended Kernel October 2022 x64 version if you haven't already (only x64 files are needed, less stable x86 ones not required) https://msfn.org/board/topic/183046-guide-vista-extended-kernel-installation/ 2. Download zipped version of PowerShell 7.2.2 (PowerShell-7.2.2-win-x64.zip) from GitHub https://github.com/PowerShell/PowerShell/releases/tag/v7.2.2 3. Extract it somewhere, from now on this somewhere is assumed to be "C:\Program Files\PowerShell\7\" so that the path to the main executable is "C:\Program Files\PowerShell\7\pwsh.exe" 4. Add this to your osver.ini in C:\Windows (if it's not there create it) [C:\Program Files\PowerShell\7\pwsh.exe] Enabled=1 MinorVersion=1 5. Add "C:\Program Files\PowerShell\7" without quotes to your system Path. To do that go to ControlPanel -> System and Maintenance -> System -> System Properties -> Advanced (it's a tab) -> Environmental Variables. Look for the Path variable and add the aforementioned path to other things after a semicolon ( ; ), thats how things are separated there. 6. Download and unzip this special shortcut https://forum.legacydev.org/viewtopic.php?f=27&t=231 and put it in "C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Accessories\Windows PowerShell" so that it appears in the start menu next to the old-school WindowsPowerShell. You can also put it in "%appdata%\Microsoft\Internet Explorer\Quick Launch" to add it to quick launch. The 2 things that are special about the shortcut I've made are: It launches cmd to launch PowerShell, which is a workaround to a problem with 7.2.2 more in why 7.2.2? It behaves like a WindowsPowerShell window, so it has a range select feature and the iconic PowerShell blue color. 7. Enjoy Why 7.2.2? So you could just install 7.2.17, 7.2.24 or any other newer 7.2.x version, and it would work fine... mostly But sometimes those versions hang on startup and never launch staying in a non-functional state which even takes a few seconds when you decide close it. On some machines like 9/10 launch tries are successful on some almost none. There are even reports of this occurring on Windows 10: https://old.reddit.com/r/PowerShell/comments/v6arrr/powershell_72x_almost_always_hangs_when_launched/?rdt=40615 https://github.com/PowerShell/PowerShell/issues/17558 But I've managed to reproduce this issue only on Windows Vista machines and multiple ones. 7.2.3 and newer as well as newer 7.1.x like 7.1.7 are affected by this issue on Vista 7.2.1 and older as well as older 7.1 and 7.0 on the other hand just fail to launch at all showing a Failed to initialize properly ... smth error. So if it wasn't for 7.2.2 you would have to go back to PowerShell 6 to get a working version But 7.2.2 has it's own issue where it sometimes immediately closes after launching an exe. Fortunately it doesn't do this when launched from another command line tool, that's why it was necessary to make a shortcut that launches cmd first and pwsh next
- 1 reply
-
1
-
- Vista x64
- Windows Vista
-
(and 2 more)
Tagged with:
-
Hello, I need your help. W7 x64 Current version is Powershell 2.0 NET 4.5 OK .NET 4.8 OK It stuck on initializing Windows6.1-KB2819745-x64-MultiPkg.msu Thank you.
-
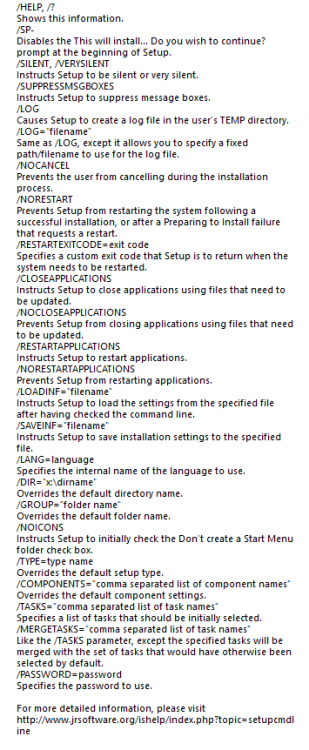
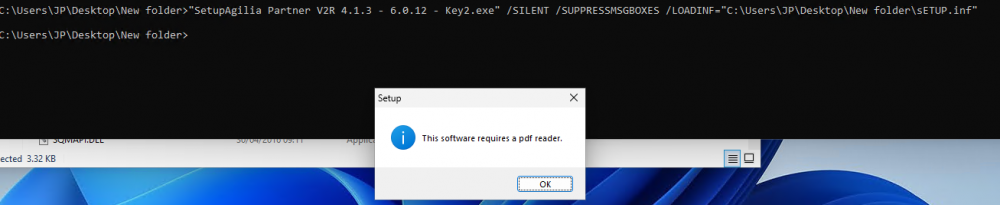
I am trying to install a application called (Agilia Partner) silently but its keep getting a pop up message(This software requires pdf reader), and when i click ok its closed and it is not installing silently. Could you please give some help. I have attached switches for the app and popup message screen shots herewith. I have tried different commands, SetupAgilia Partner V2R 4.1.3 - 6.0.12 - Key2.exe" /VERYSILENT /SP- /LOADINF="C:\Users\JP\Desktop\New folder\sETUP.inf" "SetupAgilia Partner V2R 4.1.3 - 6.0.12 - Key2.exe" /SILENT /SUPPRESSMSGBOXES /LOADINF="C:\Users\JP\Desktop\New folder\sETUP.inf"
-
- Powershell
- command
-
(and 3 more)
Tagged with:
-
Hi, I have a short code line that would ask elevated privileges for a Batch file. But now I noticed that if a file name or a folder name has an "&" character in it then the code will not work. 😫 Dose anyone have a solution for this problem? 🤔 @ECHO OFF FLTMC >NUL 2>&1 || PowerShell Start-Process -FilePath '%0' -Verb RunAs >NUL 2>&1 && EXIT /b FLTMC >NUL 2>&1 && GoTo EVD ECHO I'm not wokring. PAUSE :EVD ECHO Hallo World. PAUSE
-
Good afternoon everybody! I follow and appreciate your forum for a long time! thanks to you I was able to apply Windows server 2008 security patches to my Windows vista installation .. now I was wondering: since Powershell 3 is compatible with Windows server 2008 sp2, there is some possibility to update it also on Windows vista ? thanks to those who want to answer me!
- 5 replies
-
- Powershell
- windows
-
(and 1 more)
Tagged with:
-
Hello. I'm struggling to create a private key in order then to use to sign a PowerShell Script and I would really use some help on this. Firstly I wanted to be able to run PowerShell scripts without having to lower PowerShell's Execution-Policy and in order to do that one should have to be able to sign scripts. Therefore and after installing the Windows SDK I'm trying to create a private key (and then a certificate) in order to be able to sign scripts. But this fails likewise: C:\Program Files\Microsoft Visual Studio 8\SDK\v2.0\Bin>makecert -n "CN=PowerShell Local Certificate Root" -a sha1 -eku 1.3.6.1.5.5.7.3.3 -r -sv root.pvk root.cer -ss Root -sr localMachine Error: Can't create the key of the subject ('root.pvk') Failed And so I've begun trying to debug this, with no success. So far I've checked with these: I checked with makecert's documentation to check whether the command parameters are correct executed the command from within a non-special directory executed the command as the local Administrator user executed the command from an "elevated" Command Prompt or an "elevated" PowerShell made sure the security permissions for _ALL_ the Crypto/RSA directories are set as indicated If you have any ideas or you would like to share your insights or have me walk again over again something I've already tried/mentioned please feel free to comment. Thanks in advance.
- 14 replies
-
Hi All, We had a little bug go through our Exchange Server that really hosed our permissions on all mailboxes. I have everything working now, but am looking for a way to systematically clean up permissions. For instance: NT Authority\Self is allowed FullAccess on all mailboxes...this is good. This allows each user full access to their own mailbox. On top of this, each user is listed ALSO with FullAccess permissions on their own mailboxes. This is unnecessary due to the NT Authority\Self permission. If I were to use the Exchange Management Console to remove each user from their mailbox, EMC would actually remove their access entirely by stipulating a DENY - not good. What I am looking to do is use PowerShell to run a loop. So that you may better understand what I am trying to do: 1. Get-Mailbox2. Enumerate username associated with mailbox and assign $username variable3. Remove-MailboxPermission –user $username –AccessRight FullAccessOnce the entire command is piped: Get-Mailbox | $username = user | Remove-MailboxPermission -user $username -AccessRight FullAccess Thus, it would remove the users' full-access permissions only from their own mailbox. Can anyone help me accomplish this? I have searched and searched, but still come up empty. Thanks!